Why Wikileaks Will Kill Big Business And Big Government | The New Republic
Big claims all around.
Wednesday, December 29, 2010
Friday, December 17, 2010
Fall, 2010 - Social Research | Find Articles at BNET
Fall, 2010 - Social Research | Find Articles at BNET
Lots of articles on secrecy and privacy in government and society.
Lots of articles on secrecy and privacy in government and society.
Wednesday, December 15, 2010
Monday, December 13, 2010
These astroturf libertarians are the real threat to internet democracy | George Monbiot | Comment is free | The Guardian
These astroturf libertarians are the real threat to internet democracy | George Monbiot | Comment is free | The Guardian
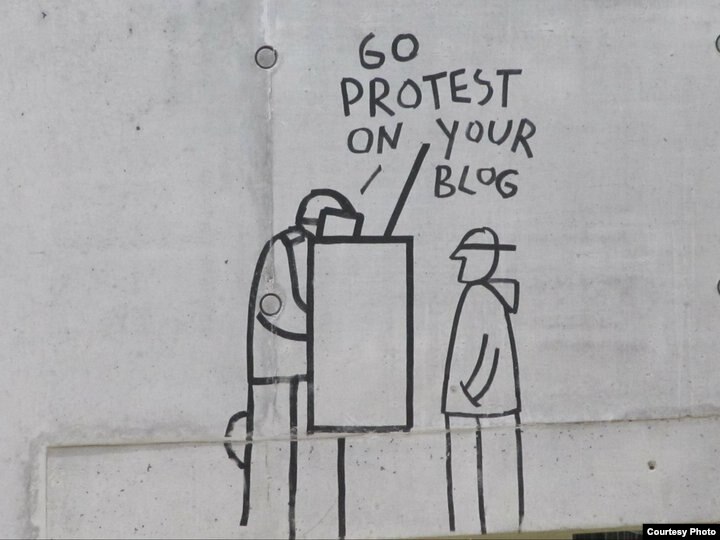
For his film (Astro)Turf Wars, Taki Oldham secretly recorded a training session organised by a rightwing libertarian group called American Majority. The trainer, Austin James, was instructing Tea Party members on how to "manipulate the medium". This is what he told them: "Here's what I do. I get on Amazon; I type in 'Liberal books'. I go through and I say 'one star, one star, one star'. The flipside is you go to a conservative/ libertarian whatever, go to their products and give them five stars … This is where your kids get information: Rotten Tomatoes, Flixster. These are places where you can rate movies. So when you type in 'Movies on healthcare', I don't want Michael Moore's to come up, so I always give it bad ratings. I spend about 30 minutes a day, just click, click, click, click … If there's a place to comment, a place to rate, a place to share information, you have to do it. That's how you control the online dialogue and give our ideas a fighting chance."
Sunday, December 12, 2010
Information overload, the early years - The Boston Globe
Information overload, the early years - The Boston Globe
But is it really so novel? Human history is a long process of accumulating information, especially once writing made it possible to record texts and preserve them beyond the capacity of our memories. And if we look closely, we can find a striking parallel to our own time: what Western Europe experienced in the wake of Gutenberg’s invention of printing in the 15th century, when thousands upon thousands of books began flooding the market, generating millions of copies for sale. The literate classes experienced exactly the kind of overload we feel today — suddenly, there were far more books than any single person could master, and no end in sight. Scholars, at first delighted with the new access to information, began to despair. “Is there anywhere on earth exempt from these swarms of new books?” asked Erasmus, the great humanist of the early 16th century.
WikiLeaks, Amazon and the new threat to internet speech - CNN.com
WikiLeaks, Amazon and the new threat to internet speech - CNN.com
...
What is troubling and dangerous is that in the internet age, public discourse increasingly depends on digital spaces created, owned and operated by private companies. The result is that one politician has more power than ever to shut down controversial speech unilaterally with one phone call.
...
As far as the law is concerned, Amazon is off the hook. Speech within the kingdom of Amazonia -- run by its sovereign Jeff Bezos and his board of directors with help from the wise counsel and judgment of the company's executives -- is not protected in the same way that speech is constitutionally protected in America's public spaces.
The law gives Amazon the right to set its own rules. The company's terms of service clearly state that it "reserves the right to refuse service, terminate accounts, remove or edit content in its sole discretion." By clicking "agree," the customer has legally consented to "represent and warrant that you own or otherwise control all of the rights to the content," and that said content "will not cause injury to any person or entity."
Thursday, December 9, 2010
Hackers Defend WikiLeaks, Testing Online Speech - NYTimes.com
Hackers Defend WikiLeaks, Testing Online Speech - NYTimes.com
The ripples from the WikiLeaks affair just keep growing and serve as a challenge not just to diplomacy but the companies of the wider web.
The ripples from the WikiLeaks affair just keep growing and serve as a challenge not just to diplomacy but the companies of the wider web.
Wednesday, December 8, 2010
LRB · John Lanchester · Let Us Pay
LRB · John Lanchester · Let Us Pay
Good reading on the plight of newspapers in the era of the web.
Good reading on the plight of newspapers in the era of the web.
Saturday, December 4, 2010
WikiLeaks: WikiLeaks degenerates into gossip | The Economist
WikiLeaks: WikiLeaks degenerates into gossip | The Economist
This Economist article seems to be spot on.
But, in a digital world, can we now assume that anything we say in confidence is really in confidence and will not find its way to some unintended audience, or that that unintended audience already has a way of reading this information. It is likely that we--in some ways--just have to accept a new openness because it is here already.
This Economist article seems to be spot on.
Diplomatic cables are something entirely different. It's part of the nature of human communication that one doesn't always say the same thing to every audience. There are perfectly good reasons why you don't always tell the same story to your boss as you do to your spouse. There are things Washington needs to tell Riyadh to explain what it's just told Jerusalem and things Washington needs to tell Jerusalem to explain what it's just told Riyadh, and these cables shouldn't be crossed. There's nothing wrong with this. It's inevitable. And it wouldn't make the world a better place if Washington were unable to say anything to Jerusalem without its being heard by Riyadh, any more than it would if you were unable to tell your spouse anything without its being heard by your boss.
But, in a digital world, can we now assume that anything we say in confidence is really in confidence and will not find its way to some unintended audience, or that that unintended audience already has a way of reading this information. It is likely that we--in some ways--just have to accept a new openness because it is here already.
Thursday, December 2, 2010
WikiLeaks, Amazon and the new threat to internet speech - CNN.com
WikiLeaks, Amazon and the new threat to internet speech - CNN.com
Very interesting piece on the Amazon / WikiLeaks issue. The article focuses on two cases where Senator Lieberman has asked material to be removed from web servers -- once YouTube and in the present case Amazon -- but with different results.
Very interesting piece on the Amazon / WikiLeaks issue. The article focuses on two cases where Senator Lieberman has asked material to be removed from web servers -- once YouTube and in the present case Amazon -- but with different results.
Amazon's dumping of WikiLeaks at one senator's request brings into stark relief one of the core problems Americans have grappled with since before our country even existed: Where is the right balance between security, on one hand, and civil liberties, on the other?
With WikiLeaks, Amazon shows its power over customers - Computerworld
With WikiLeaks, Amazon shows its power over customers - Computerworld
When we talked in class about the question of whether WikiLeaks would make government more or less open, we did not know about this action by Amazon. However, it is interesting to note that the WikiLeaks crisis has forced open actions like this, making a big company like Amazon show how much it relies or is willing to bend to pressure from the government.
On a related issue, John Doyle speculates in this morning's Globe and Mail about the cancellation of a CBC TV show -- Intelligence -- and speculates that it may have had a political connection.
from John Doyle The Globe and Mail
When we talked in class about the question of whether WikiLeaks would make government more or less open, we did not know about this action by Amazon. However, it is interesting to note that the WikiLeaks crisis has forced open actions like this, making a big company like Amazon show how much it relies or is willing to bend to pressure from the government.
On a related issue, John Doyle speculates in this morning's Globe and Mail about the cancellation of a CBC TV show -- Intelligence -- and speculates that it may have had a political connection.
The context of the U.S. memo about Canadian TV is a pervasive U.S. worry, if not outright indignation, about how these shows “feed long-standing negative images of the U.S.” So who cancelled Intelligence? The CBC, the minority Conservative government or the U.S. embassy? Or all three?
from John Doyle The Globe and Mail
Wednesday, December 1, 2010
In Awe of Google (Social Studies Blog)
In Awe of Google (Social Studies Blog)
A follow up on the NYT piece commented on earlier about how terrible customer reviews only helped one businessman improve his sales.
It turns out Google was able to make very rapid changes to its system to fix this problem, at least in part.
A follow up on the NYT piece commented on earlier about how terrible customer reviews only helped one businessman improve his sales.
It turns out Google was able to make very rapid changes to its system to fix this problem, at least in part.
Tuesday, November 30, 2010
Online, Anonymity Breeds Contempt - NYTimes.com
Online, Anonymity Breeds Contempt - NYTimes.com
This is a thoughtful piece on the dangers of anonymity on the web, and it certainly makes valid points, and raises clear examples of places where anonymity allows people to do all sorts of ugly things.
However, there is another side to the argument. There are times when anonymity allows people the freedom to speak the truth and to challenge authority. It is just a question of knowing what types of anonymity we need to keep and which we are better off without.
This is a thoughtful piece on the dangers of anonymity on the web, and it certainly makes valid points, and raises clear examples of places where anonymity allows people to do all sorts of ugly things.
However, there is another side to the argument. There are times when anonymity allows people the freedom to speak the truth and to challenge authority. It is just a question of knowing what types of anonymity we need to keep and which we are better off without.
Monday, November 29, 2010
News Desk: Cable Traffic: WikiLeaks, Facebook, and You : The New Yorker
News Desk: Cable Traffic: WikiLeaks, Facebook, and You : The New Yorker
Lots of interesting thoughts about WikiLeaks are coming out, but many of them turn out to be reflections on our own dependence on and trust of others who may not be as trustworthy or whose systems may not be as secure as we would like them to be, or as they claim they are. It is a good moment to reflect on our own personal information management practices.
The State Department is a social network, and accusing Assange of treason (never mind that he’s not an American citizen) is screaming privacy foul on a national scale. So is the White House’s condemnation of WikiLeaks. At the same time, the Times reports that these very same diplomats have been asked to commit privacy fouls themselves:One cable asks officers overseas to gather information about “office and organizational titles; names, position titles and other information on business cards; numbers of telephones, cellphones, pagers and faxes,” as well as “internet and intranet ‘handles’, internet e-mail addresses, web site identification-URLs; credit card account numbers; frequent-flier account numbers; work schedules, and other relevant biographical information.”
Whether you buy WikiLeaks’ justification for releasing the cables and whether you accept the arguments by the Times’s Bill Keller and other top editors about why they published and reported on the cables will be popular debates among bloggers and guests on cable TV and talk radio. But it almost doesn’t matter. Today, massive amounts of data can be collected, stored, and mined. We still harbor the illusion that many of our conversations are private or ephemeral, but the company that now owns my very first ISP could have fifteen years of my e-mail on its servers; my instant messages are all logged; my voice-mail messages are now audio files that can be forwarded and archived; my photographs and even my word-processing documents are moving into the cloud. It may be harder today to guarantee that you are having a private conversation than it was in the Soviet Union.
Read more http://www.newyorker.com/online/blogs/newsdesk/2010/11/cable-traffic-wikileaks-facebook-the-cloud-and-you.html#ixzz16iYZtW1B
Lots of interesting thoughts about WikiLeaks are coming out, but many of them turn out to be reflections on our own dependence on and trust of others who may not be as trustworthy or whose systems may not be as secure as we would like them to be, or as they claim they are. It is a good moment to reflect on our own personal information management practices.
Sunday, November 28, 2010
Search Engine Land: Must Read News About Search Marketing & Search Engines
Search Engine Land: Must Read News About Search Marketing & Search Engines
Google’s “Gold Standard” Search Results Take Big Hit In New York Times Story
November 28, 2010 at 5:08 pm ET by Danny Sullivan
The New York Times has a great, detailed story out today about a merchant with an unusual marketing strategy: be mean to customers. Any publicity, even negative publicity, means a win with Google’s ranking algorithms. Is he right? Maybe. Certainly the story illustrates the fallacy of Google’s “gold standard” search results. Rank Well With Bad [...]
Both the NYT article -- http://www.nytimes.com/2010/11/28/business/28borker.html?_r=1 and the article on Search Engine Land are worth reading
Google’s “Gold Standard” Search Results Take Big Hit In New York Times Story
November 28, 2010 at 5:08 pm ET by Danny Sullivan
The New York Times has a great, detailed story out today about a merchant with an unusual marketing strategy: be mean to customers. Any publicity, even negative publicity, means a win with Google’s ranking algorithms. Is he right? Maybe. Certainly the story illustrates the fallacy of Google’s “gold standard” search results. Rank Well With Bad [...]
Both the NYT article -- http://www.nytimes.com/2010/11/28/business/28borker.html?_r=1 and the article on Search Engine Land are worth reading
US embassy cables: The job of the media is not to protect the powerful from embarrassment | Simon Jenkins | Comment is free | The Guardian
US embassy cables: The job of the media is not to protect the powerful from embarrassment | Simon Jenkins | Comment is free | The Guardian:
Simon Jenkins article summarizing what we have learned so far from the latest WikiLeaks release.
"Clearly, there is no longer such a thing as a safe electronic archive, whatever computing's snake-oil salesmen claim. No organisation can treat digitised communication as confidential. An electronic secret is a contradiction in terms."
Simon Jenkins article summarizing what we have learned so far from the latest WikiLeaks release.
Wednesday, November 24, 2010
Do music artists fare better in a world with illegal file-sharing? — Times Labs Blog
Do music artists fare better in a world with illegal file-sharing? — Times Labs Blog
Interesting data analysis brom the Times Labs (it is interesting that this part of the Tunes is not behind a paywall (yet)). Perhaps this data is only true for Britain, but it does show that certain things in the music industry have not changed for the worse for music creators as the recording industry lobby groups would have us believe.
Interesting data analysis brom the Times Labs (it is interesting that this part of the Tunes is not behind a paywall (yet)). Perhaps this data is only true for Britain, but it does show that certain things in the music industry have not changed for the worse for music creators as the recording industry lobby groups would have us believe.
Sunday, November 14, 2010
Online Tracking Company RapLeaf Profiles Users by Name - WSJ.com
Online Tracking Company RapLeaf Profiles Users by Name - WSJ.com
More from the Wall Street Journal on personal privacy issues. It is clear from this article just how much information can be amassed about individuals by private companies like RapLeaf, and also makes clear the power of groups who hire this type of company to target individuals. It is a kind of dystopian future not too difficult to imagine where politicians and advertisers are able to target unique hopes or fears or vulnerabilities or worse in order to get you to act in specific ways.
More from the Wall Street Journal on personal privacy issues. It is clear from this article just how much information can be amassed about individuals by private companies like RapLeaf, and also makes clear the power of groups who hire this type of company to target individuals. It is a kind of dystopian future not too difficult to imagine where politicians and advertisers are able to target unique hopes or fears or vulnerabilities or worse in order to get you to act in specific ways.
RapLeaf knows even more about Mrs. Twombly and millions of other Americans: their real names and email addresses.
This makes RapLeaf a rare breed. Rival tracking companies also gather minute detail on individual Americans: They know a tremendous amount about what you do. But most trackers either can't or won't keep the ultimate piece of personal information—your name—in their databases. The industry often cites this layer of anonymity as a reason online tracking shouldn't be considered intrusive.
RapLeaf says it never discloses people's names to clients for online advertising. But possessing real names means RapLeaf can build extraordinarily intimate databases on people by tapping voter-registration files, shopping histories, social-networking activities and real estate records, among other things.
The Internet needs peacekeepers. Is Canada ready? - The Globe and Mail
The Internet needs peacekeepers. Is Canada ready? - The Globe and Mail
Reading this article does not necessarily convince one that it is "peacekeepers" that the web needs; however, it needs something, and it does highlight that Canada is developing some expertise in the area through the citizenlab and other ventures. But, the message is clear that cyber-espionage (and less-so cyberwar) are being carried out by many governments. Here is a case I have not read about before:
Reading this article does not necessarily convince one that it is "peacekeepers" that the web needs; however, it needs something, and it does highlight that Canada is developing some expertise in the area through the citizenlab and other ventures. But, the message is clear that cyber-espionage (and less-so cyberwar) are being carried out by many governments. Here is a case I have not read about before:
EARLIER THIS YEAR, one of the biggest law firms in Canada came under attack. Staff members began receiving e-mails that appeared to be from one of the firm’s partners, who was working on a major international M&A deal. The e-mail’s author cited confidential details of the deal, and instructed recipients to open an attached file.
The file turned out to be a form of malware, giving the e-mail’s real author access to the infected computers. When the law firm began investigating the incident, 20 computers were believed infected. The investigation eventually turned up 500 infected machines.
The law firm contacted a Toronto-based company called Digital Wyzdom, which specializes in investigating such attacks. Daniel Tobok, Digital Wyzdom’s President, says his firm soon traced the attacks to an alarming source -- the malicious e-mails originated from government servers in Asia. Indeed, the servers belonged to the government of the nation where the deal was taking place -- and that government opposed the deal. (Mr. Tobok would not identify his client or the nature of the deal).
Two years ago, Mr. Tobok says such cases -- in which a foreign government played a part, or appeared to play a part, in a cyber attack -- made up about 1 to 5 per cent of Digital Wyzdom’s business. Today, it makes up 10 to 15 per cent of cases.
“Governments are starting to realize that this is a vehicle for making things happen,” Mr. Tobok says of such government-assisted cyber attacks.
“Honestly, unless criminal charges are pressed or our government gets involved through political channels, there’s not much that can be done about it.”
The Great Cyberheist - NYTimes.com
The Great Cyberheist - NYTimes.com
This is a long article on the case of Albert Gonzalez, who was mentioned in one of our presentations last week.
The article is long but makes fascinating reading. It could be made into a movie, and could be titled something like "The Anti-Social Network" but the themes would be similar to those of the Facebook movie. A brilliant central character taking advantage of and betraying friends and colleagues, and behind the mysterious motivation for his actions is no clear answer.
This is a long article on the case of Albert Gonzalez, who was mentioned in one of our presentations last week.
Gonzalez, law-enforcement officials would discover, was more than just a casher. He was a moderator and rising star on Shadowcrew.com, an archetypal criminal cyberbazaar that sprang up during the Internet-commerce boom in the early 2000s. Its users trafficked in databases of stolen card accounts and devices like magnetic strip-encoders and card-embossers; they posted tips on vulnerable banks and stores and effective e-mail scams. Created by a part-time student in Arizona and a former mortgage broker in New Jersey, Shadowcrew had hundreds of members across the United States, Europe and Asia. It was, as one federal prosecutor put it to me, “an eBay, Monster.com and MySpace for cybercrime.”
The article is long but makes fascinating reading. It could be made into a movie, and could be titled something like "The Anti-Social Network" but the themes would be similar to those of the Facebook movie. A brilliant central character taking advantage of and betraying friends and colleagues, and behind the mysterious motivation for his actions is no clear answer.
During the legal proceedings, the court ordered Gonzalez to undergo a psychological evaluation. “He identified with his computer,” the report reads. “It is hard, if not impossible, even at the present for Mr. Gonzalez to conceptualize human growth, development and evolution, other than in the language of building a machine.”
The Great Cyberheist - Values-Based Hacking
The Great Cyberheist - NYTimes.com
In the NYTimes account of the work of Albert Gonzalez and his crew of hackers an instance of what might be called "values-based" action on the part of one of Gonalez's hacker colleagues, Stephen Watt.
Even among thieves there can be honour or actions determined by a set of values.
In the NYTimes account of the work of Albert Gonzalez and his crew of hackers an instance of what might be called "values-based" action on the part of one of Gonalez's hacker colleagues, Stephen Watt.
Gonzalez urged Watt and Toey to experiment with SQL. Watt wasn’t interested. “I had objections to what he was doing on a moral level — and on top of that, I took an intellectual exception,” Watt says. “If Albert said we were going to go after the Church of Scientology or Blackwater, I would have dove in headfirst.” Toey, however, said he felt he owed Gonzalez. He began poking around on the sites of businesses that seemed vulnerable — or for which he had a philosophical distaste. “I just didn’t like what they did,” he said of the clothing chain Forever 21. The clothes were poorly made, he said, and the employees poorly paid. “It’s just everything I hate about this country in one store.”
Even among thieves there can be honour or actions determined by a set of values.
Wednesday, November 10, 2010
What They Know - WSJ
What They Know - WSJ
The Wall Street Journal has this article -- part of a series -- on the issue of online privacy that we were discussing this week. It includes a cool interactive graph. And it will probably convince you never to visit dictionary.reference.com
The Wall Street Journal has this article -- part of a series -- on the issue of online privacy that we were discussing this week. It includes a cool interactive graph. And it will probably convince you never to visit dictionary.reference.com
Tuesday, November 9, 2010
How Canada became an open data and data journalism powerhouse | News | guardian.co.uk
How Canada became an open data and data journalism powerhouse | News | guardian.co.uk
Article about the open data initiatives in Canada and some journalists and others who are making use of the data released to create maps and tools.
magine if you took the historic records of everyone who died in the first world war. Then you matched them to one area to see how it had been affected. Or if you wanted to see if one part of your city had an epidemic of bedbugs. Or if you wanted to find out where the most guns are.
This is the work of data journalist Patrick Cain, quietly and methodically producing strikingly interesting maps of his home city of Toronto.
Article about the open data initiatives in Canada and some journalists and others who are making use of the data released to create maps and tools.
Sunday, November 7, 2010
Steal this book: The loan arranger | The Economist
Steal this book: The loan arranger | The Economist:
An Economist article on ebook and ebook readers.
If you own a physical book, in much of the world you may sell it, lend it—even burn or bury it. You may also keep the book forever. Each of those characteristics is littered with footnotes and exceptions for e-books. We are granted an illusion of ownership, but may read only within the ecosystem of hardware and software supported by the bookseller with sometimes additional limitations imposed by publishers.
An Economist article on ebook and ebook readers.
Generation Why? by Zadie Smith | The New York Review of Books
Generation Why? by Zadie Smith | The New York Review of Books:
Zadie Smith's interesting review of the movie The Social Network and Jaron Lanier's You are not a gaget. For me, this is the most interesting point of Smith's reflection on the book and the movie. But, it is still a debatable point. Yes, the system needs us to put in data that it can use. But are we the sum of what the system sees? Is what we input into a system that the system can see, the sum total of what we put in? I don't really think so.
“Information systems,” he writes, “need to have information in order to run, but information underrepresents reality” (my italics). In Lanier’s view, there is no perfect computer analogue for what we call a “person.” In life, we all profess to know this, but when we get online it becomes easy to forget. In Facebook, as it is with other online social networks, life is turned into a database...
Zadie Smith's interesting review of the movie The Social Network and Jaron Lanier's You are not a gaget. For me, this is the most interesting point of Smith's reflection on the book and the movie. But, it is still a debatable point. Yes, the system needs us to put in data that it can use. But are we the sum of what the system sees? Is what we input into a system that the system can see, the sum total of what we put in? I don't really think so.
Friday, November 5, 2010
Professional climate change deniers' crusade continues - environment - 02 November 2010 - New Scientist
Professional climate change deniers' crusade continues - environment - 02 November 2010 - New Scientist
a different kind of hactivism from the story above...
Books such as Merchants of Doubt by science historians Naomi Oreskes and Erik Conway have detailed how front groups for the fossil-fuel industry have been waging an orchestrated, well-funded campaign against climate science and climate scientists for more than two decades. Hacking into the CRU's email was simply the latest skirmish in this war against science, timed to forestall any progress towards lowering carbon emissions at the Copenhagen climate conference being held about a month later.
a different kind of hactivism from the story above...
Anonymous DDoS Attacks Crash U.S. Copyright Office Website - NYTimes.com
Anonymous DDoS Attacks Crash U.S. Copyright Office Website - NYTimes.com
Continuing its campaign against the defenders of copyright law, Anonymous orchestrated a denial-of-service attack against the website of the U.S. Copyright Office today, knocking the site offline for half an hour and rendering it slow to unusable for a couple of subsequent hours.
Online Learning Is Growing on Campus - NYTimes.com
Online Learning Is Growing on Campus - NYTimes.com
If you are thinking about writing a report on the topic of online classes, this is an interesting piece to read. It gives examples of universities which have made use of online classes as a solution to financial problems and lack of classroom space.
If you are thinking about writing a report on the topic of online classes, this is an interesting piece to read. It gives examples of universities which have made use of online classes as a solution to financial problems and lack of classroom space.
Thursday, November 4, 2010
Mark Zuckerberg: The iPad Isn't Mobile
Mark Zuckerberg: The iPad Isn't Mobile
Facebook is trying to make the most of the mobile market and to place itself not just on people's virtual (computer life) but also in their mobile every day real life. And tablet devices may not be at the top of their list right now as crucial areas of development.
Meanwhile, Jemima Kiss at the Guardian has some interesting facts about Facebook's strategy for reaching the next half billion users. She quotes some stats, including
Facebook is trying to make the most of the mobile market and to place itself not just on people's virtual (computer life) but also in their mobile every day real life. And tablet devices may not be at the top of their list right now as crucial areas of development.
Facebook is still trying to figure out its approach and strategy for tablet devices. Because tablets are a new form factor, it requires a new approach.
Meanwhile, Jemima Kiss at the Guardian has some interesting facts about Facebook's strategy for reaching the next half billion users. She quotes some stats, including
1) Mobile use is surprisingly 60% through mobile browsers, rather than apps, though 15% is through SMS.
2) Most active mobile users are in Indonesia, South Africa, Kenya, Canada and the US, where at least 60% of Facebook users spend just as much time on a mobile device as on the desktop.
Slashdot News Story | Do Firefox Users Pay More For Car Loans?
Slashdot News Story | Do Firefox Users Pay More For Car Loans?
It turns out that online retailers consider that your choice of web browser tells them something about who you are, and offers you deals accordingly.
Slashdot has this story of different car loan rates pitched to clients based on browser preference.
It turns out that online retailers consider that your choice of web browser tells them something about who you are, and offers you deals accordingly.
Slashdot has this story of different car loan rates pitched to clients based on browser preference.
A commenter on the article claims to have been previously employed by Capital One, and writes: If you model the risk and revenue of applicants, the type of browser shows up as a significant variable. Browsers do predict an account's performance to some degree, and it will affect the rates you will view. It isn't a marketing test. I was still a bit dubious, but at least one of her previous comments backs up her claims to have worked for a credit card company.
Inside the Google Books Algorithm - Alexis Madrigal - Technology - The Atlantic
Inside the Google Books Algorithm - Alexis Madrigal - Technology - The Atlantic
Books are different from the web, but Google is trying to find ways to make its book search tool as effective as its web search engine.
Books are different from the web, but Google is trying to find ways to make its book search tool as effective as its web search engine.
Rich Results is the latest in a series of smaller front-end tweaks that have been matched by backend improvements. Now, the book search algorithm takes into account more than 100 "signals," individual data categories that Google statistically integrates to rank your results. When you search for a book, Google Books doesn't just look at word frequency or how closely your query matches the title of a book. They now take into account web search frequency, recent book sales, the number of libraries that hold the title, and how often an older book has been reprinted.
Thursday, October 28, 2010
A Sentiment Detector That Reads the Social Web For You | Fast Company
A Sentiment Detector That Reads the Social Web For You | Fast Company
To follow up on what we were talking about last time, here is an article on a company that helps other companies understand what is being said about them.
Visible Technologies, a service that helps companies track what's said about them on the Web, unveiled a major upgrade today. Its new Google-inspired architecture better distinguishes the relevance and the sentiment of the mountains of social media conversations. It aims to help businesses make sense out of the cacophony of the social Web, and clients Microsoft, FedEx, Dr Pepper Snapple Group, and others are all clients of the service.
Visible has been around for a while, and has plenty of competition (we recently wrote about Trendrr, for instance). But the latest iteration of Visible's platform, called Visible Intelligence, has been built from the ground up. It has a scalable, Google-like architecture that can render tens of millions of blog posts, tweets, and forum entries within seconds.
To follow up on what we were talking about last time, here is an article on a company that helps other companies understand what is being said about them.
Tuesday, October 26, 2010
Dawn of a New Day « Ray Ozzie
Dawn of a New Day « Ray Ozzie:
What happens after the PC? Will the complexity of PC technology, i.e. the complexity of Microsoft Windows, essentially doom it? Is the answer a number of smaller connected services, like apps, each carrying out small tasks that together cover our information processing needs?
"it’s important that all of us do precisely what our competitors and customers will ultimately do: close our eyes and form a realistic picture of what a post-PC world might actually look like, if it were to ever truly occur. How would customers accomplish the kinds of things they do today? In what ways would it be better? In what ways would it be worse, or just different?"
What happens after the PC? Will the complexity of PC technology, i.e. the complexity of Microsoft Windows, essentially doom it? Is the answer a number of smaller connected services, like apps, each carrying out small tasks that together cover our information processing needs?
Sunday, October 24, 2010
The Yale Digital Commons
The Yale Digital Commons
One of the possible topics for your longer final research projects is or could be an analysis of networking technologies or tools that could be useful to university students at Dal or elsewhere. I came across this page -- the Yale Digital Commons page http://commons.yale.edu/ which describes the tools available to students at Yale. Here is the description from their page:
One of the possible topics for your longer final research projects is or could be an analysis of networking technologies or tools that could be useful to university students at Dal or elsewhere. I came across this page -- the Yale Digital Commons page http://commons.yale.edu/ which describes the tools available to students at Yale. Here is the description from their page:
The Yale Digital Commons is a collection of online tools for students and faculty in Yale College and the Graduate School of Arts and Sciences. The tools can be used to create things such as websites, blogs, wikis and databases for teaching and learning.
Sunday, October 17, 2010
The Way We Live Now - Little Brother is Watching - NYTimes.com
The Way We Live Now - Little Brother is Watching - NYTimes.com:
Perhaps. Perhaps the technology that has dictated that this is "the way we live now" is a prison we choose to live inside. It is the technology which forces us to be in the spotlight, and forces us to be individuals.
Clementi, unlike Orwell’s Winston Smith, who hid from the telescreens whenever possible and understood that the price of personhood was ceaseless self-censorship and vigilance, had no way of knowing that the walls had eyes. Nor did his unseen observer anticipate the ultimate consequences of his intrusion.
In “1984,” the abolition of personal space was part of an overarching government policy, but nowadays it’s often nothing more than a side effect of wired high spirits.
Ours is a fragmentarian society, infinitely divided against itself and endlessly disrupted from within by much the same technologies that, in Orwell’s somber novel, assured a dull and deadening stability. In some ways, his nightmare vision of state control is cozy and reassuring by comparison. Big Brother may have stifled dissent by forcing conformity on his frightened subjects, but his trespasses were predictable and manageable. What’s more, his assaults on citizens’ privacy left the concept of privacy intact, allowing the possibility that with his overthrow people might live again as they once had.
Perhaps. Perhaps the technology that has dictated that this is "the way we live now" is a prison we choose to live inside. It is the technology which forces us to be in the spotlight, and forces us to be individuals.
Friday, October 15, 2010
MPAA Copy-Protected DRM Site Hacked By Anonymous | TorrentFreak
MPAA Copy-Protected DRM Site Hacked By Anonymous | TorrentFreak:
Perhaps it is a war after all.
--
"A site run by the MPAA has become the most recent victim of cyber attacks being carried out by Anonymous. CopyProtected.com, a site used to inform on copy protection and DRM on DVD and Blu-ray movie discs, now displays a missive from the anarchic group . After a few seconds it redirects visitors to the homepage of The Pirate Bay."
Perhaps it is a war after all.
--
Tuesday, October 12, 2010
The ‘Legal Blackmail’ Business: Inside a P2P-Settlement Factory | Epicenter | Wired.com
This summary is not available. Please
click here to view the post.
Elevator Pitch: BraveNewTalent does recruitment - Generation-Y style | Media | guardian.co.uk
Elevator Pitch: BraveNewTalent does recruitment - Generation-Y style | Media | guardian.co.uk:
"Lucian Tarnowski has a big idea - he thinks recruitment is a sector ripe for disruption and is reinventing it for Generation Y through BraveNewTalent.com. Next on his hitlist is education, which he thinks is 'no longer fit for purpose'."
Interesting interview with someone who thinks he can use social networking to change the way people look for work and the way companies look for employees.
--
"Lucian Tarnowski has a big idea - he thinks recruitment is a sector ripe for disruption and is reinventing it for Generation Y through BraveNewTalent.com. Next on his hitlist is education, which he thinks is 'no longer fit for purpose'."
Interesting interview with someone who thinks he can use social networking to change the way people look for work and the way companies look for employees.
--
Labels:
social networking
Thursday, October 7, 2010
Can copyright bill survive with all its kinks? - The Globe and Mail
Can copyright bill survive with all its kinks? - The Globe and Mail:
This article from the Globe gives a good account of the various sides in the current debate over the proposed copyright law. It makes clear the difficulty of arriving at a law that will please everyone.
"Don’t hold your breath. The good news is that Bill C-32, the government’s proposed copyright reform, should go to second reading and a parliamentary committee this fall to get the kinks ironed out before it becomes law. The bad news is that the kinks are complicated and pessimists wonder how this will ever get to third reading before an election is called and it dies on the order paper."
This article from the Globe gives a good account of the various sides in the current debate over the proposed copyright law. It makes clear the difficulty of arriving at a law that will please everyone.
Tuesday, October 5, 2010
Twitter and Facebook cannot change the real world, says Malcolm Gladwell | Books | The Observer
Twitter and Facebook cannot change the real world, says Malcolm Gladwell | Books | The Observer:
A piece from the Guardian discussing Malcolm Gladwell's article in the New Yorker: "Small Change: Why the revolution will not be tweeted". Gladwell makes the distinction between social movements held together by "strong ties," that is a close friendship between participants, and online social networks which tend to be comprised by "weak ties." In many ways Gladwell is rehearsing the type of argument he made in The Tipping Point, for example, the crucial influence key connecting people had in creating a tipping point in the world. Gladwell's ultimate point is that there is a difference between a weak-tie Facebook friend and a strong-tie close personal friend. While he acknowledges that remarkable things can be done by tapping into the latent power of weak-tie relationships, he keeps his focus on the failure of incapacity of social networks to be effective in practice. Interestingly, Gladwell argues that social movements are most effective when they are organized as a hierarchy. He argues that "Al Qaeda was most dangerous when it was a unified hierarchy. Now that it has dissipated into a network, it has proved far less effective." As we talked about in class, the effectiveness of a network is determined by how effectively it works together to achieve the program that holds together the various nodes. It seems to me that Gladwell is saying that networks are inherently comprised of weak ties where individual nodes have only a weak connection to the central program. This seems to be a weakness in the argument--something where other evidence may cast a different light on the ideas.
Read more http://www.newyorker.com/reporting/2010/10/04/101004fa_fact_gladwell?currentPage=all#ixzz11UMVhwOR
"Gladwell is a spirited contrarian. His argument in the New Yorker was an attack on the prevalent idea that online social networks represent the future of campaigning and protest, and perhaps – in totalitarian states – of revolution. The bestselling author of The Tipping Point unpicked this notion with typical chutzpah, moving quickly from emotive and carefully selected individual case studies to sweeping universal principles.
Gladwell examined the most effective mass protest of modern times – the American civil rights movement. Using an account of the courageous coffee bar sit-in in Greensboro, North Carolina in 1960, he argued that such activism was based on the strength of intimate friendships and shared experience, and directed by hierarchical power, could never have arisen from the 'weak ties' and 'horizontal' associations that characterise the campaigning of online 'friends' and 'followers'."
A piece from the Guardian discussing Malcolm Gladwell's article in the New Yorker: "Small Change: Why the revolution will not be tweeted". Gladwell makes the distinction between social movements held together by "strong ties," that is a close friendship between participants, and online social networks which tend to be comprised by "weak ties." In many ways Gladwell is rehearsing the type of argument he made in The Tipping Point, for example, the crucial influence key connecting people had in creating a tipping point in the world. Gladwell's ultimate point is that there is a difference between a weak-tie Facebook friend and a strong-tie close personal friend. While he acknowledges that remarkable things can be done by tapping into the latent power of weak-tie relationships, he keeps his focus on the failure of incapacity of social networks to be effective in practice. Interestingly, Gladwell argues that social movements are most effective when they are organized as a hierarchy. He argues that "Al Qaeda was most dangerous when it was a unified hierarchy. Now that it has dissipated into a network, it has proved far less effective." As we talked about in class, the effectiveness of a network is determined by how effectively it works together to achieve the program that holds together the various nodes. It seems to me that Gladwell is saying that networks are inherently comprised of weak ties where individual nodes have only a weak connection to the central program. This seems to be a weakness in the argument--something where other evidence may cast a different light on the ideas.
Read more http://www.newyorker.com/reporting/2010/10/04/101004fa_fact_gladwell?currentPage=all#ixzz11UMVhwOR
Labels:
networks,
social networking
Saturday, October 2, 2010
Mobile internet will outstrip 'desktop' use by 2014, says ex-Obama adviser | Technology | guardian.co.uk
Mobile internet will outstrip 'desktop' use by 2014, says ex-Obama adviser | Technology | guardian.co.uk:
While the headline is about the growth of the mobile internet, Castells also comments about social networks and the impact they have had:
- Sent using Google Toolbar"
While the headline is about the growth of the mobile internet, Castells also comments about social networks and the impact they have had:
"Speaking about the 'phenomenal' societal impact of the emergence of social networks, Castells said the number of users – 500m on Facebook alone – is only at 'the tip of the iceberg'. 'The deepest social transformation of the internet came in the last decade with social networks,' he said, adding:'Increasing sociability, increasing happiness, an increasing feeling of being autonomous – all this relates to use of internet. The most important thing in this is that it's not anonymous – this is real people doing real things, sharing things. They're not just friends, they're contacts also. They're doing things together, they're not just chatting.
'Social networks are living spaces. People share with limited emotional effort. This is a constantly networked world that evolves with human experience, and individuals choose the terms of their co-evolution. Entrepreneurs build these sites, not corporations. The important thing is that even if people go into these sites, they can't do whatever they want. People will create another and take all their friends with them. The entry barriers are so low, the capital [outlay is] almost nothing, and [the barriers to entry are] so diffused.
'If Facebook becomes nasty people disappear. This is constructed by individuals who organise, and their companies are in the business of selling freedom – if they don't give it people go away. This is transforming social movements and politics,' Castells said.
- Sent using Google Toolbar"
Stuxnet worm heralds new era of global cyberwar | Technology | The Guardian
Stuxnet worm heralds new era of global cyberwar | Technology | The Guardian:
The Guardian has this detailed story on the whole issue of cyber war which we suddenly think of in a different way this week.
Charles Arthur posted this video of a "generator tearing itself apart after a cyberattack, in this case part of a test.
Is cyberwarfare a genuine threat?
--
"In recent testimony to Congress, Alexander underlined how the cyber war threat had rapidly evolved in the past three years, describing two of the most high-profile attacks on countries: a 2007 assault on Estonia, and a 2008 attack on Georgia during its war with Russia, both blamed on Moscow.
Those were 'denial of service' attacks that disabled computer networks. But it is destructive attacks such as Stuxnet that frighten Alexander the most."
The Guardian has this detailed story on the whole issue of cyber war which we suddenly think of in a different way this week.
Charles Arthur posted this video of a "generator tearing itself apart after a cyberattack, in this case part of a test.
Is cyberwarfare a genuine threat?
--
Monday, September 27, 2010
News Analysis - Stuxnet Worm Is Remarkable for Its Lack of Subtlety - NYTimes.com
News Analysis - Stuxnet Worm Is Remarkable for Its Lack of Subtlety - NYTimes.com:
A more detailed report on the Stuxnet worm. While the information now being discovered about this attack gives us a glimpse of strategies of a cyber war, the Worm itself apparently fails in that it was not focused enough and that it was discovered at all.
“Proliferation is a real problem, and no country is prepared to deal with it,” said Melissa Hathaway, a former United States national cybersecurity coordinator. The widespread availability of the attack techniques revealed by the software has set off alarms among industrial control specialists, she said: “All of these guys are scared to death. We have about 90 days to fix this before some hacker begins using it.”
The ability of Stuxnet to infiltrate these systems will “require a complete reassessment” of security systems and processes, starting with federal technology standards and nuclear regulations, said Joe Weiss, a specialist in the security of industrial control systems who is managing partner at Applied Control Solutions in Cupertino, Calif.
One big question is why its creators let the software spread widely, giving up many of its secrets in the process.
A more detailed report on the Stuxnet worm. While the information now being discovered about this attack gives us a glimpse of strategies of a cyber war, the Worm itself apparently fails in that it was not focused enough and that it was discovered at all.
Saturday, September 25, 2010
In Court? Be Careful What You Post! | Courtroom Strategy by Attorney Oscar Michelen
In Court?
Litigants in a court case beware! Your adversary may be allowed to view all of your postings, including private and deleted ones, if they bear any relation to the court case. In the first case of its kind yesterday, a Suffolk County NY Judge, in Romano v. Steelcase, Inc., allowed a defendant in a personal injury lawsuit to obtain access to the Facebook profile of the plaintiff suing them. The court held that since the plaintiff put her physical health at issue by suing, she could not restrict the defendant from obtaining evidence that might support or contradict her claims. Supreme Court Judge Allen Spinner reasoned -I think completely correctly – that social networking sites are not private lockboxes where you store your most intimate secrets; in fact their privacy policies tell you that they are public spaces. Therefore he said:
“Plaintiff has no legitimate reasonable expectation of privacy.”
Even deleting stuff seems to be no protection from the long arm of the law.
Be Careful What You Post! | Courtroom Strategy by Attorney Oscar Michelen:
Litigants in a court case beware! Your adversary may be allowed to view all of your postings, including private and deleted ones, if they bear any relation to the court case. In the first case of its kind yesterday, a Suffolk County NY Judge, in Romano v. Steelcase, Inc., allowed a defendant in a personal injury lawsuit to obtain access to the Facebook profile of the plaintiff suing them. The court held that since the plaintiff put her physical health at issue by suing, she could not restrict the defendant from obtaining evidence that might support or contradict her claims. Supreme Court Judge Allen Spinner reasoned -I think completely correctly – that social networking sites are not private lockboxes where you store your most intimate secrets; in fact their privacy policies tell you that they are public spaces. Therefore he said:
“Plaintiff has no legitimate reasonable expectation of privacy.”
Even deleting stuff seems to be no protection from the long arm of the law.
Labels:
personal privacy
Google Warning Gmail users on China Spying Attempts
Google Warning Gmail users on China Spying Attempts
China hacking or spying or something else?
Google is using automated warnings to alert users of its GMAIL messaging service about wide spread attempts to access personal mail accounts from Internet addresses in China. The warnings may indicate wholesale spying by the Chinese government a year after the Google Aurora attacks or simply random attacks. Victims include one leading privacy activist.
Warnings appeared when users logged onto Gmail, encountering a red banner reading "Your account was recently accessed from China," and providing a list of IP addresses used to access the account. Users were then encouraged to change their password immediately. Based on Twitter posts, there doesn't seem to be any pattern to the accounts that were accessed, though one target is a prominent privacy rights activist in the UK who has spoken out against the Chinese government's censorship of its citizens
China hacking or spying or something else?
Labels:
network security
Iran Fights Strong Virus Attacking Computers - NYTimes.com
Iran Fights Strong Virus Attacking Computers - NYTimes.com:
Iran's government announces that it is fighting a computer virus:
Iran claims that this is "part of the electronic warfare against Iran" and an attempt to disrupt its nuclear program.
Iran's government announces that it is fighting a computer virus:
"But the announcement raised suspicions, and new questions, about the origins and target of the Stuxnet virus, which computer experts say is a far cry from common viruses that have affected the Internet for years.
Stuxnet, which was first publicly identified several months ago, is aimed solely at industrial equipment made by Siemens that controls oil pipelines, electric utilities, nuclear facilities and other large industrial sites. While it is not clear that Iran was the main target — the infection has also been reported in Indonesia, Pakistan, India and elsewhere — a disproportionate number of computers inside Iran appear to have been struck, according to reports by computer security monitors."
Iran claims that this is "part of the electronic warfare against Iran" and an attempt to disrupt its nuclear program.
Labels:
cyberwarfare
Friday, September 24, 2010
Where Good Ideas Come From
An introduction to Steven Johnson's new book Where Good Ideas Come From, Johnson is also the author of Everything Bad Is Good for You.
Even if you may disagree with his ideas, you can enjoy the animation.
Labels:
creative spaces,
innovation,
networks
Thursday, September 23, 2010
Blogging your blogs
I am starting a blog here as a way of following the blogs that you--MGMT 3601 bloggers--create.
Subscribe to:
Comments (Atom)